Last month I found myself in Google: Is weed in Nevada legal? This was the day after arriving in Renault for Wild West Hacking Festival – Way West 2021. I kept noticing that the hotel smelled like it from the moment we arrived. I attended one of the first security conventions to have a personal experience, as Covid-19 turned everything off. It would be a hybrid model, with many webinars and people to attend in practice. I had just started a new job with Secure Ideas as a security consultant, and here I flew over the Sierra Nevada to attend my first conference.
I have listed some of the highlights, mandatory and surprises I took away from this wild ride.
Laboratory rat
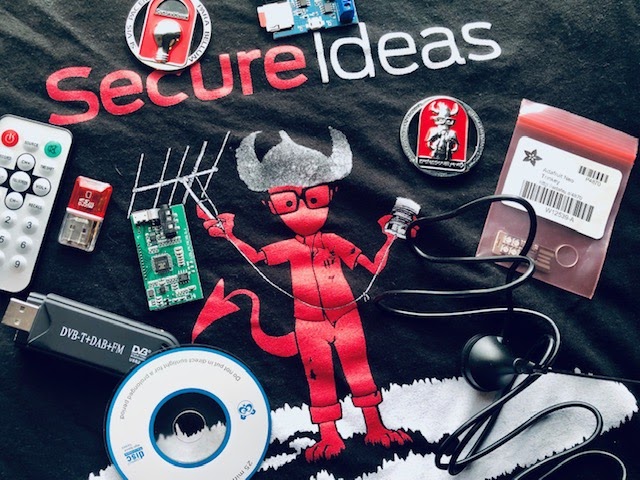
The practice labs were really great and I would love to spend more time in this area. The bag included a pile of equipment that matched the labs. You can learn about RFID signals, software-defined radio, wireless input devices and other amazing nonsense. I was really intrigued by the SPT and how I could have fun with it. I mentally noted how I could join the police radio when I got home so I could be this person in the neighborhood. No matter what conference you attend, I highly recommend visiting the labs.
Kevin knows everyone
This particular horse is hosted by John Strand, owner of Black Hills Information Security. John Strand was a man I have admired and watched for some time. It also happens to be a longtime friend of Kevin Johnson, our CEO at Secure Ideas. When Kevin heard that John was one of the reasons I became interested in this field, he invited me to attend the conference, even though I was only at work for a few weeks. Secure Ideas was a sponsor and Kevin was one of the speakers.

As soon as we entered Nugget, Kevin began to encounter people he knew, which gave me the opportunity to meet many of the people whose careers I follow. There was a steak dinner at the hotel on Thursday night, which was included in the ticket price. Here I realized that he was one of the people at our table Alice Miller. She was one of the speakers I wanted to see on Friday, a huge name and someone I admired a lot. There are only a handful of famous women in cybersecurity and it is definitely OG. She is also from Milwaukee, Wisconsin. It’s always going to trigger something in my Midwestern lizard’s brain (since I grew up in the Chicago area) that just assumes they’re good people and we’re going to be BFF. One of my colleagues, Ohaun, also mentioned that we save space for Wolf. Wolfgang Görlich? Have dinner with Alice and Wolf? Another legend and he lives in Michigan. I was so lucky that I thought I should play the slots. However, I may have set that $ 100 on fire.
Keep talking
The first night there was a welcome speech by John Strand, followed by a keynote from Paul Vicki. On Thursday morning there was a main note from Josh Wright. Then I went to talk to Corey Overstreet from Red siege. It was a really difficult decision because it was at the same time as Dave Kennedywe’re talking next door. Talk to Kevin – Konami Code: The secret code to enable your SDLC security he was super informative and funny as usual, although he will tell you that he is a terrible public speaker. Overall, I think my favorite talk of delusion was Thursday afternoon from Jason Downey with Red Siege. It was entitled – Six things Nobody [email protected]# $ ing told me about Pentesting. Jason has been testing for about 8 months. This really resonates with me because I am new to pentesting and it gave me a lot of idea what to expect. There was also a main note from Naomi Buckwalter, interviews with Alyssa Miller, Wolf Goerlich, Marily Vernon, and CEO of Red Siege; Tim Medin. Not only did I learn a lot, but it also gave me a good sense of how closely connected, useful, and brilliant people in the industry are.
Wishing for sushi
While I was in Reno, I offered to make a few engagement calls for the office. I did it between conversations on Friday. The first few calls were easy. My trick was borrowed from another consultant and probably used often. I was from IT and had to run some updates, blah blah blah, a confusing technical talk. Most people were suspicious and said they were busy, they would have to call me and then they took my name. And yes, I used my real name. It only took me one call to realize that pronouncing my own name during a greeting was so ingrained that it would be more of a struggle to use a fake name than it was worth. The name I was going to use was literally written in front of me and I still deleted mine.
If someone ever calls you with a request for a username and password, personal or company information, money or access to your computer, it is a scam or a scam. You absolutely have to take their name and number and escalate them. It is exactly what to do. What you don’t need to do is call someone who left you a message that they are from IT and continue to give them full access to your machine. Which is exactly what happened with one of the calls I made. You have to tell yourself that you are helping to protect your customers, because it is terrible to deceive someone in this way. If you ever feel bad in Renault, comfort yourself with a great sushi. It turns out that they have a wonderful sushi due to the proximity to the coast of California and this was a very welcome surprise.
You can’t see everything
I saw so much, but not almost everything. Seminars, talks, escape room, more labs, CTF, even Backdoors and breakthroughs tournament. There were only about 200 people in person, and that was perfect for my first crook. I felt intimate and managed to meet so many talented, amazing people. The bigger one, like Defcon with 25,000+ attendees I doubt that would be possible. I highly recommend planning your days in advance once you know the schedules.
It should be mentioned
- One of our consultants from Charlotte, North Carolina (Ohaun) won the bull ride and was great.
- I’m listening Darknet Logs # 67 – The Big House to learn more about John Strand and the Black Hills.
- You should also visit BHIS training pages for more great stuff from John.
- Follow the links to all the people and websites I mentioned if you are new to the industry.
- If you are in a hotel full of hackers, I would like to think that they are all a variety of white hats. However, make sure your phone and laptop are encrypted and your passwords are strong. This is good everyday advice, not just in a hotel full of hackers.
- Yes, marijuana is legal in Nevada.

If you are on the fence to attend a conference, I would urge you to go. It was a great time and something I think everyone at infosec should experience at least once. Although I plan to go to much, much more.
The message 1st series of a new consultant – Hackin Fest of Wild West – Way West 2021 appeared first on Professionally evil insights.
*** This is a syndicated blog of the Security Bloggers Network from Professionally evil insights author of Katie Collins. Read the original post at: http://blog.secureideas.com/blog/2021/07/a-new-consultants-1st-con-wild-west-hackin-fest-way-west-2021.html
