Story
April 26, 2022

Virtualization software and model-based design provide a path that not only enables system designers to maintain legacy software for avionics and other mission-critical systems but also makes it possible to migrate that code to modern higher-performance processing platforms, for example from an older PowerPC-based VME board over to a new x86 or Arm-based VME or OpenVPX module.
For embedded defense and aerospace systems, the most expensive element is rarely the underlying hardware. Actually, the most expensive part is the valuable application software that runs on the hardware. In many cases the hardware, whether the semiconductor devices such as the processor or the module form factor in use, will become obsolete long before the software running on that hardware loses its value. The challenge has been how to reliably and cost-effectively retain the investment in critical legacy software code when the life of the hardware it was originally designed to run on has come to an end.
Virtualization software can enable system designers to reap the advantages that enterprise virtualization and layers of cyber hardening bring to real-time embedded systems. Such an approach enables weapons systems to decouple software from specific hardware configurations and combat obsolescence. This approach makes it possible to protect older application software with contemporary cybersecurity protections that weren’t available when the code was first written. Northrop Grumman’s Real-time Virtualization And Modernized Protection (ReVAMP) software enables a secure enclave execution environment that delivers a layer of protection from outside threats. Secure boot and modern hardware-supported encryption are available once the legacy software runs in a ReVAMP virtual environment.
For embedded avionics applications, programs can now move trusted and proven applications from legacy Compact PCI, VXS, or similar form factors, to a contemporary VME, OpenVPX, or XMC module to improve the performance of avionics systems and drastically reduce sustainment costs.
Because the software enables system designers to effectively future-proof their software systems by virtualizing the obsolete hardware currently being used, without changing a single line of the original application’s code, it’s possible to extend the life of critical real-time software so that it can run exactly as first written, but on new hardware. Virtualization software also makes it possible to add modern functionality, performance, and capabilities to an older system while maintaining the original application software. Since the original application code is not changed, the high cost and significant risks of having to port or rewrite legacy code in order to migrate it to modern hardware are eliminated.
The virtualization software is used to emulate the original system at the hardware level. New capabilities can then be added by writing new software in the legacy environment or in the modern environment. Once the system is emulated, interfaces provide the means for new software written in a modern language to interact with the legacy software.
If, for example, an updated Identification Friend or Foe (IFF) transponder is required, the new code used to deal with that separate transponder capability can be added to the original application code through a process called “thunking.” This process involves the software designer essentially “jumping” out of the current execution of the legacy application and operating system to execute the newly written IFF code, and then jumping back into the application code where they left off, while still maintaining critical timing requirements. “Thunk” code can be used to either enhance or completely replace a section of legacy code.
A virtualized system is also capable of handling any I/O interfaces used by the legacy software. An I/O layer called Emulated I/O Services (EIOS) enables the user to remap I/O. If a legacy serial port interface was used on the obsolete hardware, and the new infrastructure requires data to be communicated over Ethernet, the I/O layer provides the necessary mapping between legacy serial and Ethernet. The I/O layer extracts data at the interface layer, so the legacy code continues to operate with no required changes. (Figure 1.)
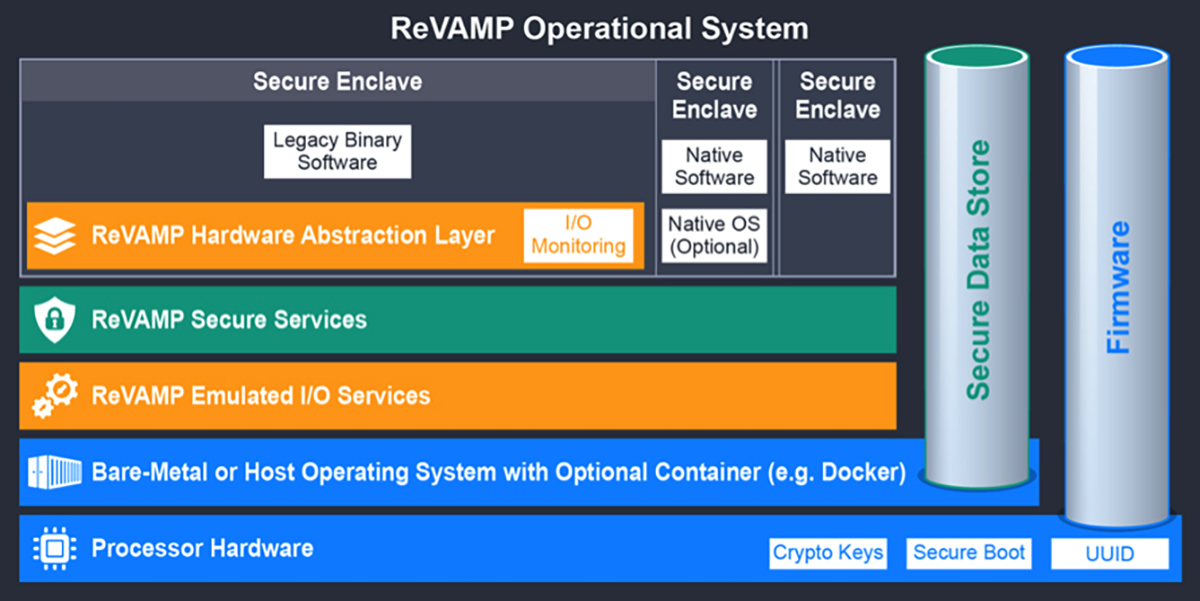
[Figure 1 | A block diagram of virtualization software architecture.]
The software took a digital model-based approach and implemented a new technique for modeling a processor architecture that eliminates the need to create a new emulator from scratch. The digital model is built first, without needing knowledge of the target environment in which the emulator will run. After the model of the legacy system is completed, it’s run through the engine with the particular end-state target architecture as an input. For example, if the new target platform for an obsolete PowerPC board is x86-based, the model is run through the model’s engine to generate an emulator that will run on that x86 target platform. The same model can be used to generate emulators for dissimilar target platforms.
As an example, if an x86 card is running a ReVAMP emulator and that x86 card is going to be upgraded to an Arm processor, the model does not need to be rebuilt since the model is stored in a library. The engine simply needs to be set for the appropriate new target board and Arm architecture in order to generate an emulator that will run on that target Arm platform. This approach enables software to continuously migrate to newer hardware platforms as needed, thus allowing weapon system owners to more clearly understand – and accurately project – life cycle costs.
The virtualization approach used in ReVAMP was first developed in the late 1990s to support the Air Force Research Lab (AFRL); the earlier tool has been updated and enhanced with mitigation for contemporary cybervulnerability concerns. The software is deployed on a wide range of programs including DoD aircraft, electronic warfare (EW) pods, missile warning radars, and in numerous other mission-critical environments. In one example application involving a mission computer for a US Navy platform, the approach was able to consolidate 188 different cards to just four VME modules for a command-and-control system that was having significant hardware obsolescence. In that case, the system’s MTBF [mean time between failures] went from around 127 hours to approximately 22,000 hours, without changing a single line of the legacy code.
Another aim of the software is towards use in a virtual-software integration lab (V-SIL). Today, many customers have reduced resources and are seeking ways to gain efficiencies, reduce testing time, and increase the throughput of their labs in order to speed upgrades and modifications for weapon systems. Since ReVAMP can virtualize the entire system, it can provide a digital twin of a system that can be used for multiple lab testing scenarios with exactly the same operational flight program (OFP) that is deployed on the aircraft or ground system.
To help bring the benefits of this virtualization software – the main ones being obsolescence mitigation and technology refresh – to the defense and aerospace market, avionics buyers can use ReVAMP technology on products in many different form factors, including VME, 3U/6U VPX and XMC boards, and a range of processor types including NXP Power Architecture, Intel, and Arm architectures. (Figure 2.)

[Figure 2 | The VME-1910 is an example of a modern VME single-board computer that can be used with ReVAMP to modernize legacy systems. Curtiss-Wright photo.]
Russell Obert is senior manager, Security, Messaging and Modernization Product Center for Northrop Grumman Defense Systems. Since joining Northrop Grumman in 1988, previous assignments have included Operating Unit Director for the Air Command and Control Operating Unit; Program Director for the London Metropolitan Police Service command and control system upgrade; Director of Strategic Initiatives for the Civil Systems Division; and Manager of Product Engineering for the Public Safety Products line of business. He earned a bachelor’s degree in electrical and computer engineering and a master’s degree in electrical engineering from the University of Colorado at Boulder; Russ also maintains Project Management Professional certification from the Project Management Institute.
Denis Smetana is a senior product manager for FPGA and DSP products for Curtiss-Wright Defense Solutions, based out of Ashburn, Virginia. He has more than 30 years of experience with ASIC and FPGA product development and management in both the telecom and defense industry and more than 15 years of experience with COTS ISR products. He has a BS in electrical engineering from Virginia Tech.
Northrop Grumman Defense Systems
https://www.northropgrumman.com/
Curtiss-Wright Defense Solutions
https://www.curtisswrightds.com/








