SDR for Assessing Wireless Device and Network Security
By Brendon McHugh and Kaue Mocellas
Software-defined radio (SDR) is not only capable of performing such threats, but it also provides means to expose vulnerabilities in the physical (PHY) layer of protocol stacks. In this article, we discuss various means for assessing/debugging device security using SDRs. The discussion includes RF fuzz testing using software on an SDR, which allows for both debugging low-level RF and hardware protocols and PHY/MAC analysis; and penetration testing, where wireless receivers are spoofed or attacked to assess vulnerability. By using SDRs, these techniques can be easily accomplished by developing algorithms in GNU Radio and/or Python.
Why the U.S. Needs a Unified Cybersecurity Framework
It’s Not Too Early to Prepare for 6G
Tech-Based Hybrid Warfare: The Need for Endpoint Cybersecurity
RF Device Vulnerabilities
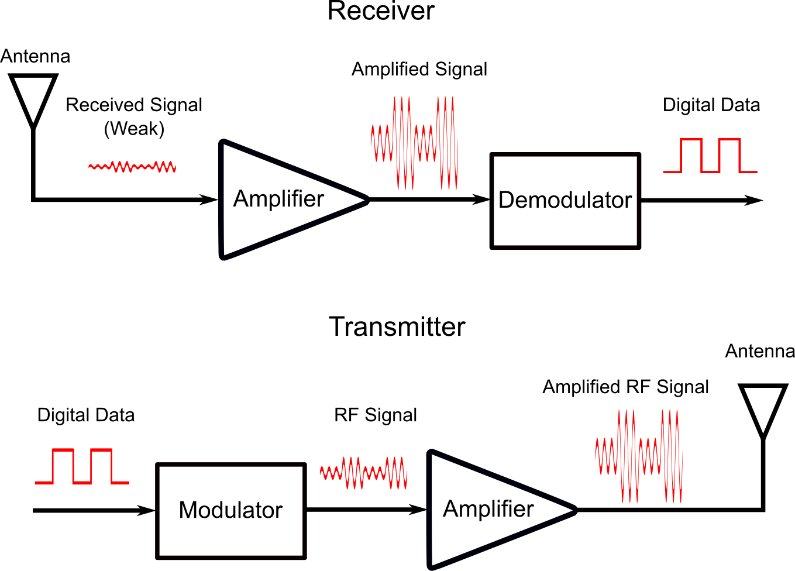
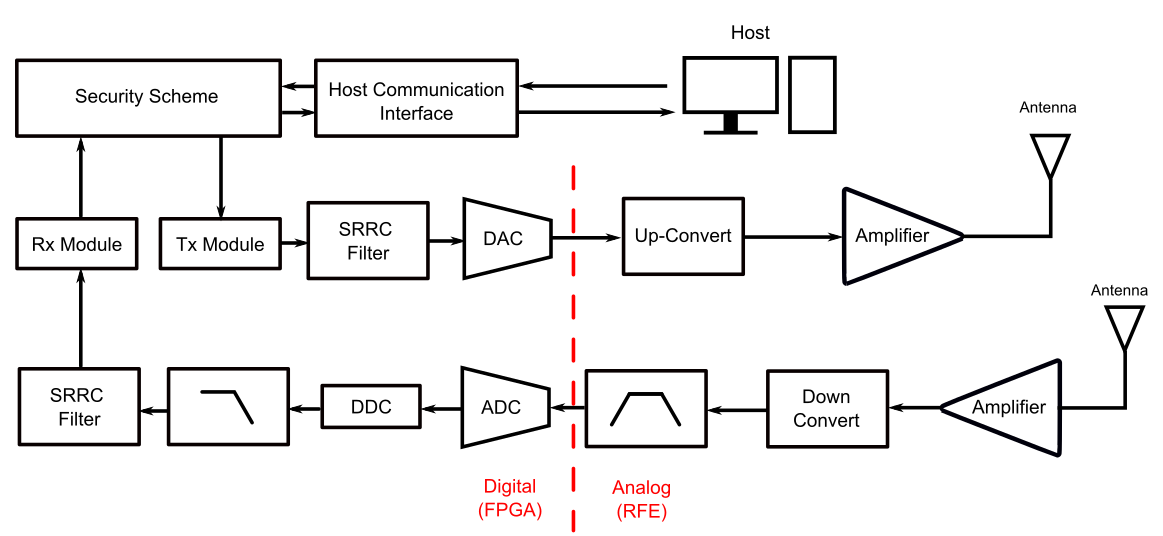
RF signals are a fundamental part of wireless communication, being applied in satellite signals (GPS), mobile network towers, LAN modems for Wi-Fi, and everyday gadgets, such as garage door controllers. The principle is quite simple: a modulated carrier signal is used to transmit information through electromagnetic waves. There are several modulation techniques in both the market and scientific literature, including amplitude shift keying (ASK), quadrature amplitude modulation (QAM), and phase shift keying (PSK). The general configuration of a RF transmitter and receiver are shown in Figure 1. In the receiver, a signal is received by the antenna, amplified to obtain a manageable amplitude and demodulated to extract the information. At the transmitter side, the carrier is modulated using digital data, amplified to optimize RF transmission, and sent to the antenna.
Because RF signals are not bounded to a constrained physical media, they are available over the air and can be easily picked up by anyone with an antenna and receiver, creating a very risky scenario for malicious threats. This problem was amplified by the quick evolution of receivers and demodulators, that have become inexpensive to the average user in a way that virtually anyone can intercept and track RF signals. Moreover, Bluetooth Low Energy (BLE) and IoT communication protocols have only recently been adopted by the industry, so the security developers and tools are not yet completely prepared for devices with several RF input/outputs. Some examples of radio-based device vulnerabilities are the Philips Hue vulnerability (Zigbee Worm), the Keysniffer, the SweynTooth, the BlueBorne exploit, the BleedingBit, and the Mouse Jack.
Common RF Attacks
The most obvious attack in RF-based communication systems is espionage. It consists of detecting, reading (eavesdropping) and monitoring wireless devices for malicious purposes. It can used to obtain private information about individuals, through interception of mobile phones, wearables and health performance monitors. Moreover, the highly interconnected IoT infrastructure of modern companies is a critical vulnerability, as virtually any compromised IoT device can serve as a gateway for leaking confidential information and gaining access to the company’s network. To put it into perspective, even wireless mice and keyboards can be used to access remote PCs, by using an attack called MouseJack, which works by sending false packages of commands to exploit the unencrypted USB dongles and take over the victim’s computer.
The problem becomes even more critical in the context of industrial IoT (IIoT). This term is being widely used in the technology industry to designate a highly interconnected structure of sensors, actuators, computers, and manufacturing equipment communicating with each other in a wireless manner. Common attacks in IIoT structures include device hijacking, data extraction and denial of service. The first attack, device hijacking, describes the unauthorized control of an IoT device by a malicious party. Data extraction, also called data siphoning, is an attack with the intent of obtaining confidential data that is transmitted through the IIoT network. Finally, the denial of service attack is used to render endpoint devices and the network itself inoperable by flooding the communication links with useless data traffic.
In any case, network attacks will always exploit the architecture of the wireless network implemented in the IIoT structure, so it is important to contextualize the attacks with the most common wireless technologies in the industry. One of the most used technologies today is Long Range (LoRA), which is a low-power WAN (LPWAN) technology that uses a modulation scheme based on chirp spread spectrum. LoRA is used in several industrial applications, including smart meters, detection and tracking, IoT networks, smart agriculture and climate monitoring. Other examples of technologies are cellular networks, including 4G/LTE and 5G and Zigbee, which is used to create mesh networks based on the Advanced Encryption Standard (AES)-128 encryption scheme. Particularly concerning cellular networks, the IIoT market is divided between LTE-M and narrowband IoT (NB-IoT). Furthermore, the global navigation satellite system (GNSS)/GPS access required by several IoT devices in the industry can be used in spoofing and jamming attacks, causing malfunctions and compromising basic operations.
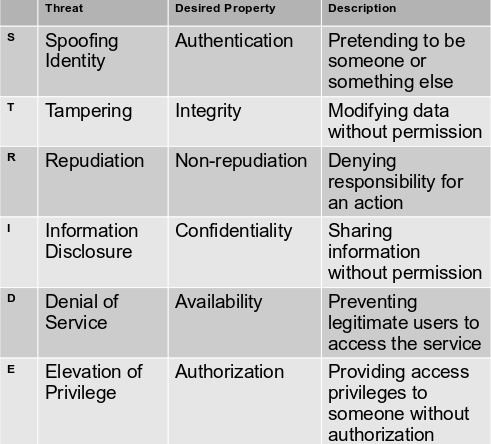
To better understand and be prepared to RF attacks, it is important to implement a model to classify and describe the threats. This model can be combined with a model of the network system to help decision-making and threat detection/classification. One of the most used systems is the STRIDE model, which is described in Table 1. The STRIDE model classifies threats into six different categories, with each one jeopardizing a specific network property that is desired in the system. By categorizing the security threats in the IoT network using STRIDE, we are able to identify potential schemes to prevent and mitigate their effects before they happen. The table below shows a description of each STRIDE threat, and the property that will be compromised if the attack concretizes. In an IoT perspective, the description of each threat should be contextualized to the application. For instance, in RFID based systems, an attack aiming to modify the serial number in a tag to match the one of another person is classified as tampering, and tracking someone’s position through the use of RFID tags falls under the information disclosure category.
SDRs for Attacking Wireless Devices
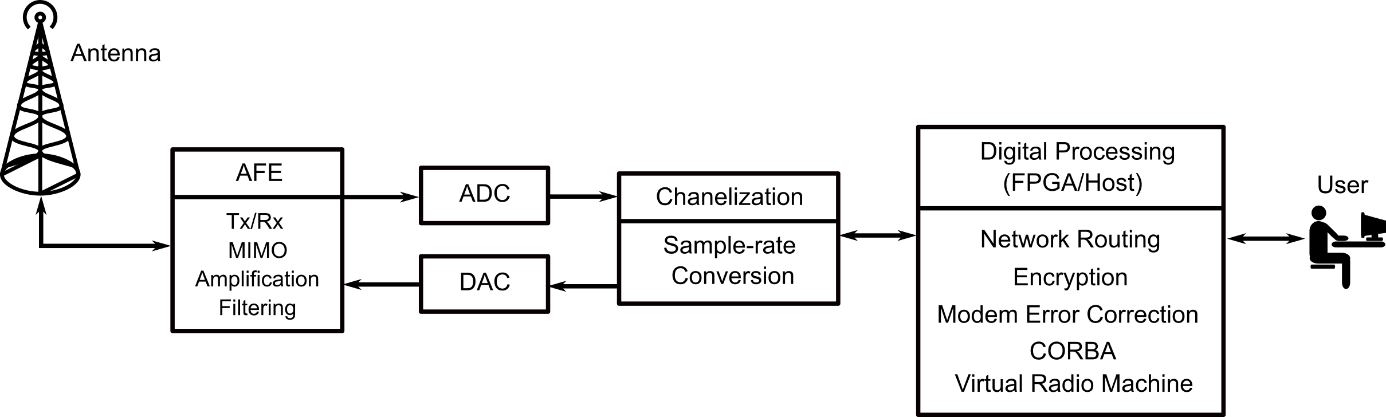
SDRs are incredible versatile radio devices that perform most of the complex computing operations in the software side instead of the hardware. The advent of SDRs was a switch in the analog radio paradigm that significantly improved the flexibility, reliability, robustness and cost benefit of complex and well-structured radio systems. SDRs can be designed in a variety of form factors, ranging from USB dongles to full 3U rack units, and several different prices, going from $10 to several hundreds of dollars. However, independent of the price and form factor, SDRs can be generally divided in three parts: the radio front-end (RFE), the digital backend and the mixed-signals interface (Figure 1). The RFE consists of the irreplaceable analog circuitry necessary to perform basic functions, such as amplification, impedance matching with the antenna, and radio tuning. The typical RFE channel is composed of a receiver (Rx) and a transmitter (Tx), and one RFE can have several channels in multiple input multiple output (MIMO) SDRs. In high-end SDRs, the RFE modules can reach 3 gigahertz of instantaneous bandwidth over multiple MIMO channels, with tuning range from near DC to 18 GHz.
The digital backend is composed of a field programmable gate array (FPGA), to perform highly parallel data computation, providing high-throughput digital signaling process (DSP) functions (channelization, sample-rate conversion) and network operations (routing, encryption, modem error correction, etc.). Moreover, the use of FPGAs allows for complete reconfiguration of the digital processing circuit without any hardware replacement by simply programming the FPGA. This means that SDRs are extremely flexible and can work with several different protocols in the same unit. This is desirable in network security testing, as the same device can be used in different networks. The digital backend also communicates with the host computer, and high-end SDRs provide fast optical links (qSFP+) for high-throughput data communication. Finally, the mixed-signal interface is responsible for connecting the RFE with the digital backend, and it is performed by ADCs and DACs. Figure 1 shows the basic architecture.
Because of the programmable nature of the FPGA, SDRs can be used in RF attacks. For instance, very simple SDRs are used to hack into car key fobs by exploiting security threats in popular models. For instance, to prevent replay attacks, where the attacker copies the last code sent by the key fob, modern vehicles implement rolling code security to never use the same code twice. However, some models of Subaru don’t use any sophisticated code generator to replace the current code after use, they simply increment the code. This can be easily exploited by hackers: an SDR embedded in a USB dongle, combined with a Raspberry-Pi, can read the code sent by the original user, decode the package using the SDR, increase one unit in the code, and re-transmit the incremented code to fool the car’s receptor. Therefore, detecting and mitigating network security threats is a fundamental step in the design of any IoT device.
In a more general sense, SDRs can be used to hack into any IoT system, and the typical process can be divided into four stages:
• Capture/record. In this stage, the signal is simply measured by the RFE, digitalized, and stored in the memory cells of the digital backend.
• Demodulation. The demodulation scheme must be obtained, as well as the symbol rate and other basic communication properties. If these properties are already known, then it is easy to implement a demodulator in the SDR. If not, sophisticated algorithms, sometimes implementing artificial intelligence, must be implemented in order to retrieve the modulation scheme.
• Decode. Most confidential data is encrypted; therefore, it is important that the SDR, or the host, has means to decode the binary data after demodulation.
• Information Exploitation. Finally, the decrypted information is used to achieve a purpose. This objective can be the extraction of sensitive information, tampering with the transmitted data or using the data to gain control over the device. In the case of some car key fobs, the obtained data was used in a replay attack, where the decoded code was simply incremented and re-transmitted.
Protection, Prevention, Testing
As discussed previously, replay attacks can lead to significant threats in IoT security. The most basic algorithm to fight this threat is the rolling code algorithm, also called hopping code. It basically consists of re-generating the command code after each transmission, making it impossible for the hacker to use the old code for exploitation. The most basic rolling code algorithms use pseudorandom number generators (PRNG) in both transmitter and receiver, so that the new code can be compared. For Wi-Fi, Wi-Fi Protected Access (WPA) is the most popular algorithm. The WPA uses the temporal key integrity protocol (TKIP) as the encryption protocol, which is based on keys that change after each package transmission. The WPA2 is a variation that can implement the extensible authentication protocol (AES), which is a more sophisticated encryption scheme than the TKIP (although significantly heavier). WPA also uses the pre-shared key (PSK) encryption protocol to secure the communication line, which is simply implemented by personal passwords.
In IoT networks, especially in IIoT infrastructures, authentication is significantly more challenging, due to the heterogeneity of devices in the same mesh. Therefore, more dedicated security schemes are required. One example is authentication via time-based one-time password (TOTP), where a disposable password is generated by adding the uniqueness of the current time to a pre-shared secret key. Of course, latency and clock synchronization must be taken into account when developing TOTP bases networks.
Although it may be naive to think that an IoT network can become completely free of threats, it should be the main goal of designers. One idea is to combine more than one security protocol to increase robustness. For example, a key rolling algorithm can be combined with a two-way handshake protocol to obtain both key security and a synchronized communication line. The working principle is simple: the key rolling algorithm provides a different key after every transmission, and the two-way handshake prevents de-synchronization between transmitter and receiver by any external agents.
SDRs for Testing Device Security
One of the most popular wireless protocols is the LoRA network. It specifies the physical (PHY) layer of the network, leaving the superior layers to other technologies, such as Long Range WAN (LoRAWAN). To evaluate security of LoRA systems, the test should focus on first identifying the carrier frequency, which is in the sub-GHz range for most LoRA applications; the modulation scheme; and the encryption standard. In this context, the combination of SDRs with GNU Radio libraries provide a powerful and convenient framework to evaluate LoRA networks. Because most operations are programmed in the FPGA, the SDR can be easily adapted into any LoRA specification. The test module can capture and decode the LoRA PHY signals and implement an interpreter in GNU Radio to analyze and exploit the data.
SDRs can also be also used to perform penetration tests. These tests are intended to simulate a cyberattack against a computer or IoT device, to verify the existence of network vulnerabilities. The information obtained from the tests is then used to configure applications to overcome the potential threats and increase the network security. An interesting tool for penetration tests was developed recently using GNU Radio and the Scapy framework. The Scapy-radio is basically a generic wireless monitor/injector device, used for penetration assessment in a variety of applications. In a case study, the Scapy-radio was validated in systems using the Z-Wave wireless protocol, which is typically applied in home-automation systems. SDR-based penetration tests have also been validated in BLE and Zigbee RF protocols, showing its versatility and wide impact in the IoT community. The study concluded that SDRs are important tools for experiments involving penetration attacks.
Fuzzing, of fuzz testing, is a well-known liability verification in software. It is an automated method that simply injects random, invalid or unexpected data into the input of a software, and the outcomes are monitored to diagnose problems such as bugs, crashes and memory leaks. In a wireless network context, fuzzing can be implemented using an SDR-based module to expose the physical layer, as well as the media access control (MAC) layer of the structure, which is fundamental to find potential liabilities.
SDRs can also be implemented to evaluate the performance of the IEEE 802.15.6 standard in wireless body area networks (WBAN). WBANs is gaining a lot of traction in the IoT community, with the recent boom of wearable technology and healthcare monitoring acceptance among the public. However, the IEEE 802.15.6 accepts three different types of communication: narrowband (NB), ultrawideband (UWB) and human body communication (HBC), so different WBANs present different modulation, encryption and frequency specifications, which affects performance and makes it difficult to create a generalized evaluator for all WBAN implementations. In this case, SDRs can be extremely helpful, as the FPGA of the digital backend can be easily reconfigured to match the specifications of the WBAN under test. This means that a single off-the-shelf device can be used to evaluate virtually any WBAN implementation with minimal hardware adaptations. A generalized architecture of an SDR applied in security evaluation can be seen in Figure 4.
 ?
?
This article discussed the main aspects of network security, as well as the potential threats that can jeopardize the proper operation of wireless networks, including IoT, IIoT and mobile communication. We also discussed threat modeling using the STRIDE standard. Moreover, we reviewed the key properties of SDRs, their potential role as key agents of RF attacks and why they are so important in security testing and measuring. SDRs can be used in penetration tests, LoRA network validation, evaluation of WBAN standards and fuzz testing. SDRs are fundamental tools in the design of secure and robust wireless networks, providing flexible and reliable network algorithms to validate your security schemes. They also provide a wide variety of size, weight and power (SWaP) characteristics to comply with most RF structures. High-end SDRs are available in the market, with configurations designed to satisfy even the most demanding applications.
Would you like to comment on this story? Find our comments system below.
Brendon McHugh is a field application engineer and technical writer at Per Vices, which has extensive experience in developing, building, and integrating software defined radios. Brendon is responsible for assisting current and prospective clients in configuring the right SDR solutions for their unique needs. He possesses a degree in theoretical and mathematical physics from the University of Toronto. Kaue Morcelles is a PhD student in electrical engineering and technical writer.