Since the days of Alan Turing, the promise of a digital computer has been that of a universal machine, one that can be a word processor one minute and a robot brain the next. So why are radios, a technology even older than computers, still designed stubbornly to do one thing–like 3G, Wifi, FM, or GPS–for their entire lives?
In fact, the era of the single-purpose radio is over, says Michael Ossmann, the founder of an Evergreen, Colorado company called Great Scott Gadgets. And he believes he’s built the one cheap, hacker-friendly radio to rule them all.
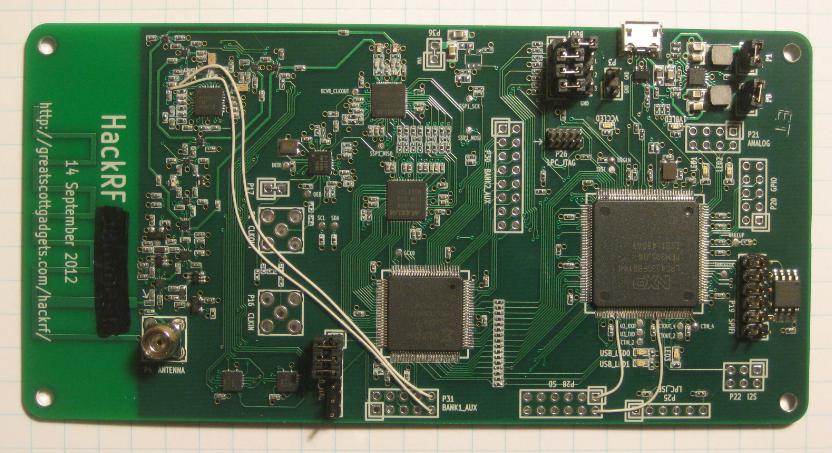
At the ToorCon hacker conference in San Diego Saturday, Ossmann and his research partner Jared Boone plan to unveil a beta version of the HackRF Jawbreaker, the latest model of the wireless Swiss-army knife tools known as “software-defined radios.” Like any software-defined radio, the HackRF can shift between different frequencies as easily as a computer switches between applications–It can both read and transmit signals from 100 megaherz to 6 gigaherz, including frequencies as low as the range used by FM radio up to the gigaherz frequencies used by Wifi or experimental wireless protocols for cars communicating in traffic. In between those bookends lies everything from police radio to cellular signals from AT&T and Verizon to garage door openers–all signals that HackRF can instantaneously intercept or reproduce. And at Ossmann’s target price of $300, the versatile, open-source devices would cost less than half as much as currently existing software-defined radios with the same capabilities.
“Pretty much any wireless device that you can think of would be in the frequency range covered by HackRF,” says Ossmann.”Just from observing [a signal] over the air, you can reverse engineer it completely to figure out the information transmitted over the network, and potentially inject your own transmissions onto that network. All of that can be done with one HackRF device and a laptop.”
With HackRF in the hands of hackers or security researchers, in other words, no wireless signal would remain secure just by virtue of using a unique, unfamiliar frequency. Ossmann says that tools like HackRF mean wireless communications will need to evolve beyond the “security through obscurity” model of protecting communications that has long been considered outmoded in the wired computing world.
But Costin argued that meant ADS-B needs more security–not that software-defined radios themselves are dangerous. “Software-defined radios are a good thing and an important tool for research,” he told me. “A knife is a good thing in the kitchen but can be abused to do bad things. SDRs are the same.”
The Pentagon, at least, seems to think software-defined radios are a promising tool. To fund the beta testing phase of HackRF, the Department of Defense research arm known as the Defense Advanced Research Projects Agency (DARPA) pitched in $200,000 last February as part of its Cyber Fast Track program.
HackRF is far from the only attempt to create an affordable software-defined radio. A device called the USRP has been available for a few years from the company Ettus Research, though it ranges in price from $800 to $2000 depending on its capabilities. Hackers have also created far cheaper models of software defined radio adapted from TV tuners that cost less than $50. But those bootleg versions have a more limited frequency range and can only receive signals, not transmit them. “HackRF fits right in the middle,” says Tom Rondeau, who manages the open-source radio software project GNU Radio. “There hasn’t been a way to transmit and receive at such a low cost, and that’s a big deal.”
Before founding Great Scott Gadgets, Ossmann honed his wireless expertise as a security researcher at the Department of Commerce’s National Telecommunications and Information Administration Lab in Boulder, Colorado, a job he described as being “the one security guy in a lab full of radio engineers.” But he says HackRF’s low cost is also largely the result of Moore’s Law: cheaper integrated circuits available only in the last few years have made the intensive computing needs software-defined radios far more accessible.
Ossmann isn’t shy about admitting the ways HackRF’s capabilities and cost could disrupt current security models for wireless communications. Better to put cheap software-defined radios in the hands of penetration testers who can demonstrate the insecurity of those communications than to reserve the technology only for better-funded attackers who would exploit the same wireless communications in secret.
But Ossmann also hopes it will be adopted by a wide spectrum of hackers and researchers who will use it for experimentation and creative purposes even he can’t predict. “If someone does something cool with HackRF and I say ‘Wow, I’ve never thought of that,'” he says, “That’s when I’ll know the project is a success.”
—
Follow me on Twitter, and check out my new book, This Machine Kills Secrets: How WikiLeakers, Cypherpunks and Hacktivists Aim To Free The World’s Information.